I have a suite of services exposed using a reverse proxy (npm) protected with passwords, but I’m always a bit nervous that username/passwords aren’t enough – is there a way to set up 2FA either on Nginx Proxy Manager side or on, e.g., the 'arr suite of apps?
You could look into apps like authelia, keycloak, authentic, etc.
authelia
Ah that sounds like exactly what I’m looking for, actually. Thanks. Any tutorial you have that you can recommend?
Yep! Authentik is my choice there, and it works flawlessly for my use-cases. The only thing that keeps me on my toes is still the celery dependency on redis that makes it not HA. They’re working on it and making me happy :)
HA?
Highly available. For example, being able to run multiple instances of it and if one server goes down the other picks up slack.
HighAvailability
This is the way, look up techno Tim’s “ssl everywhere” video to get traefik with wildcard ssl for Internet facing and local services then set up authentik and you will have a solid setup that will last for years with a solid foundation.
I have a Synology NAS (my humble server) would that work with it too??? For example the DSM page (which I don’t have exposed).
Synology’s DSM has built-in MFA support, though it also has some features for external identity management. I don’t think Keycloak and so on would be compatible though.
Yeah you are right, they already support 2FA.
I use keycloak for all by services that dont have any 2FA, I use an oauth proxy to front the service
linuxserver.io have a templates for Authelia and Authentik on nginx
Incredible. Thanks that makes this all much easier.
Not sure if it fits your requirements exactly but I just put a service behind TwinGate and it works well for my usage case. I can allow my wife secure access to services she needs to access from anywhere securely - she just opens the app to connect and she can access what she needs.
I haven’t but you can enable 2FA, as well as restricting based on things like hardware, OS and whether a device has biometrics.
If you’re comfortable with using Cloudflare, you can use their zero trust tunneling and setup an application layer that adds auth to those services. I have mine protected by my GitHub login.
Oh interesting. I’m using zero trust tunneling already to get through my ISP network chicanery. How would that work? Do yo uhave any tutorials you can recommend?
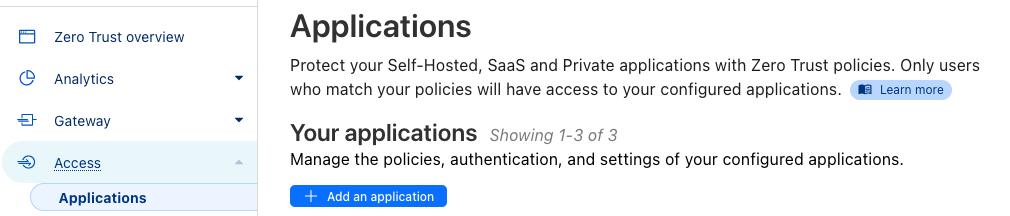
You can secure your tunnels using the Access menu and then adding an application. It should be somewhat straight-forward but you’re basically looking to create an access policy and then adding the rules you want. For example a simple one is to add an allow rule for certain emails. When you enter your email an access code will be sent to you before you can access the application resource. That’s just one of many ways to secure it using their application config and access policies.
I used to expose my Vaultwarden instance with it, but I think it didn’t work with the protected CF login.
Some systems support MFA eg vaultwarden. For that I use the built in MFA with Yubikeys.
For things that are not MFA supported but I need them to be open I put them behind Authelia and Nginx Proxy Manager.
Authelia config makes sense now. It was confusing at first however the custom config required on NPM still confuses me.
Anything else stays off the internet and I can access via vpn back into my LAN.
I used to run Authelia with NPM. It supports TOTP as second factor.
It is! I know that Mastodon and Lemmy support it. I cannot speak for any of the others though.