Economy 2.0 is next week I think (hope!) - so this is just vanilla breakage.
Glorified network janitor. Perpetual blueteam botherer. Friendly neighborhood cyberman. Constantly regressing toward the mean. Slowly regarding silent things.
- 2 Posts
- 38 Comments

 6·19 days ago
6·19 days agoThe obvious recommendation is Gentoo stage1 tarball running in Windows Linux Subsystem.
(on a serious note: whatever you’re running on your daily driver)

 9·20 days ago
9·20 days agoBeen using Nebula for a while now. Going to miss some YouTube creators, but I’ll expect to get over it.

 3·21 days ago
3·21 days agoThe rubber keyboard was pretty weird first, felt a lot like cheap pocket calculator, but once you got used to the BASIC shortcuts, you could program like a champ on it.

 26·25 days ago
26·25 days agoSo, is this the type of SLAM you’d typically see in a moshpit? Or are we talking about wrestling slams?
Ah, well. Maybe that saves a click and 10 minutes of someones life.
I notice you quoted the sentence from the description - did you watch the video itself?
No, I’m afraid I didn’t.
Every time I talk about privacy online, the pessimists always come out. "It’s impossible to have any online privacy.
My experience is actually completely opposite. While mainstream “normies” don’t seem to care, most of them are using readily available privacy tools in their communication daily. Things like WhatsApp, Signal and iMessage. Most websites these days are HTTPS enabled. Governments are so concerned about this loss of monitoring capability, they’re trying to craft laws which allow them to backdoor devices before encryption happens. And they’re meeting resistance, despite all the lobbying (see Chat Control2.0). We’ve never had as widely adopted privacy tools as we have today.
Big tech and advertising are two problems that still create trouble. A lot of this stems from completely different, non-privacy related reasons (the lax US policies concerning anti-consumer and monopoly laws) but even here policies around the world are slowly catching up. GDPR gives Europeans quite a bit of control over our data and while this is still just one baby step - it’s much better than it used to be. There’s a lot of global inequality here though. Facebook/Meta is synonymous to Internet in the developing world, because they’ve used their monopoly money to exploit the situation. Digital imperialism is still strong.
I’m not going to harp too much on SMTP privacy, Proton has a bunch of nice services. If that’s where your MX happens to point at is, then great, but we do also need to slowly move away from these old protocols that offer no privacy choice (yeah I know, SMTP is here to stay).
What I’d like to see more, is talk about threat modeling in this space. Because that’s where it all starts and threat models are quite personal. There’s no “one size fits all” privacy, because our needs vary. Political dissident living in exile from hostile government has completely different needs for privacy compared to a person who doesn’t like YouTube ads. We should try to foster easily digestible discussion around personal threat modeling - right now we (the privacy crowd) come across as loonies since lot of the advice we give starts from the wrong end of the model.
I don’t see digital privacy as a pessimistic space. But what do I know, I’m not a content creator.

 12·1 month ago
12·1 month agoWhat else am I missing?
Large scale manufacturers pre-installing Linux? Readily available multi-language support for home users? Coherent UI regardless of computer and distro underneath. Billions on lobbying money spent on politicians for favorable policy crafting? Billions spent on marketing campaigns to actually sell the idea to the masses who simply don’t care any of your points (or any technical reasons, privacy or anything else that might be top of mind of the current Linux userbase).
I’d say Linux has a good chance of capturing 5-6% of the market in the coming years if lucky (I believe we’re somewhere around 4% at the moment), unless one of the big tech monopolies decides to start throwing money into it (Like Google did with Android)

 17·1 month ago
17·1 month agoThis is the moment in Scooby-Doo where the gang unmasks the person they’ve just caught and underneath is just the Microsoft Bing logo
!environment@beehaw.org used to be cool, but it’s heating up!

 21·1 month ago
21·1 month agoThe only AI function I could see myself using is one that would summarize 15 minute youtube videos into coherent readable text in blog format. That would be nice. Especially when they’re posted like this, just links without much context.
Well, that was extremely long winded way to say “depends on your threat model”. Which it does.
So nothing new under the sun.

 7·2 months ago
7·2 months agoSo your requirement with cellular calling (eSIM) is already fairly restrictive and depends on which market we’re talking about. Where I live (.se) you get to choose between Apple and Samsung and since Apple was out of the question, you’re stuck with Samsung.
Not entirely sure if your second requirement with long battery life can be fulfilled. You’ll be charging the watch every day, probably more often if you take calls on it.
There’s some rumors that Garmin Forerunner/epix will get eSIM support, but that will be also carrier dependent.
These wearables are pretty complicated high end devices, I wouldn’t really give them to elderly parents who stuggle using a normal mobile.
I think it might be better to look into other tyoe of devices like pager systems from caregivers, if you’re worried about health issues.

 0·2 months ago
0·2 months agoThese attacks range from phishing attempts to sophisticated malware intrusions. Website defacement attacks and Distributed Denial of Service (DDoS) attacks are often seen during significant events
…
And these tactics can also be replicated elsewhere. Other countries worried about the impact of cyberattacks and disinformation campaigns on their elections and democratic institutions should be paying attention.
These tactics are already being replicated elsewhere. This has been the normal Internet background noise for years. This is not news.
However, just as in 2014 when Russia was preparing for Crimea annexation, the amount of targeted (cyber and kinetic) escalated. Same again before Ukraine invasion. That’s what we should be paying attention to - not everyday “millions of cyberattacks” or hybrid misinformation war - those are already happening. and should be handled as basic boring Internet hygiene.We should be building resilience against targeted pre-invasion cyber. We should be building ways to take down drones, we should be building robust satellite communication networks so we don’t have to rely on kindness of tech billionaires. We should find more robust ways of navigating because GPS is too easy target.
In short, we should be learning from the Ukraine conflict, which is the first (and currently only) real live theater for cyberwarfare.
I don’t and the energy consumption of public AI services is a stopper for “testing and playing around”. I think I’ll just wait until it takes over the world as advertised.

 7·2 months ago
7·2 months agoI’ve configured Firefox on their Linux laptop not to keep any cookies after the browser is closed. I know this isn’t a Linux/Firefox issue
It’s you issue.
Block third-party cookies, but allow cookies from the site itself. I’m not sure why you’d filter those out in the first place?
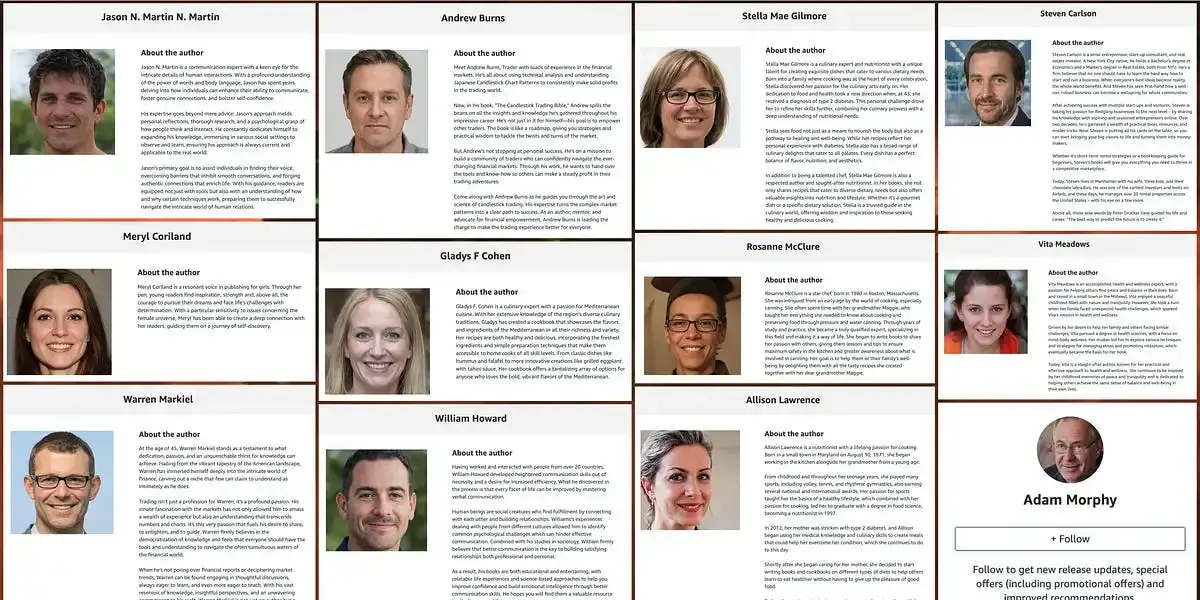
I’m a consultant so whenever I’m applying for a new gig I need to provide a consultant profile, which is very similar to resume.
Over the years I’ve learned that most customers are not very interested in the “personal stuff” sections - they just want to know you have the skills required, so try to minimize the amount of personal data and concentrate on skills and past gigs (anonymizing customers/companies) etc.
But - unfortunately you have to tell something about yourself and your ability to work together with others, there’s really no way around it. It’s also more and more customary that (for some reason) they want your photo. Stuff like education, certifications need to be there, but keep it very short. Think about “social media profile page”.
Provide stuff like contact info, address, phone, date of birth (if required) and references separately - don’t put them into your resume. You can add something like “Personal information and references provided separately by request” in there, that way, even if the document is shared, all they get is something resembling a LinkedIn profile.
You can also try to add “confidential” to the document header, but I’ve noticed it’s not respected very often.


Dr. Disrespect: I’ll fucking own this problem!
Also Dr. Disrespect: Owns up to inappropriate message exchange with a minor.
awkward_side_eye.jpg