There’s encryption and it is managed by the SIM.
- 20 Posts
- 1.18K Comments

 01·8 days ago
01·8 days agoLike what?

 11·8 days ago
11·8 days agoWindows 10 Enterprise with a ton of group polices applied, no issues ever. The Windows Terminal app is really good.

 1·8 days ago
1·8 days agoSo, Apple was right all along. WebP is a bad format.

 1·8 days ago
1·8 days agoIt is basically a SIP (a widely used VoIP standard) inside of IPSec (a type of VPN, and also a common standard). The IPSec credentials are provided by your your SIM card and that makes it about as secure as cellular.

 1·10 days ago
1·10 days agoIt’s not “my hardware” it is that everyone talks about Linux desktop yet nobody puts any effort into going into the tablet market that is where Linux can have a real advantage (because ARM + full desktop OS experience) and get a large user base.

 0·9 days ago
0·9 days agoInstead of wasting time on supporting bullshit hardware that almost nobody owns and will be forgotten in about 6 months, what about placing some effort into real hardware that real people want to use like tablets? Fucks sake.
Update: just to make it clear, I own no hardware of that type, it’s not “doesn’t work on my hardware” type of situation. It is that everyone likes to talks about Linux desktop (including Canonical) yet nobody puts any effort into going into the tablet market that is where Linux can have a real advantage (because ARM + full desktop OS experience) and get a real user base.

 1·2 months ago
1·2 months agoWhile I don’t disagree with you about the potential of those alternatives they won’t cut it for the average graphic designer… usually not due to the lack of features but most likely because of the network effects / dominant position that Adobe holds over their field. People who need to collaborate with others and are pressured to get stuff done can’t afford the slightest compatibility issue.

 11·2 months ago
11·2 months agoThe way to get Linux more appealing is to get proprietary software makers, like Adobe, Microsoft (Office), you know the actual things people need to do their job, to make software for Linux. Steam Deck is a good example of this, it works because Steam ported the games to Linux…

 1·2 months ago
1·2 months ago+1, this is poised to create issues and potentially ruin a few relationships.
OP’s sister is used to Apple services and not even other payed cloud services come close to the level of integration Apple provides. It just works, is a real thing inside the Apple ecosystem and anything the OP might get will be inferior and she will complain.
On the day the service is down or something doesn’t work / some update breaks the sync or wtv she’ll just be there with an “entitled atitude” pressuring the OP to fix things.
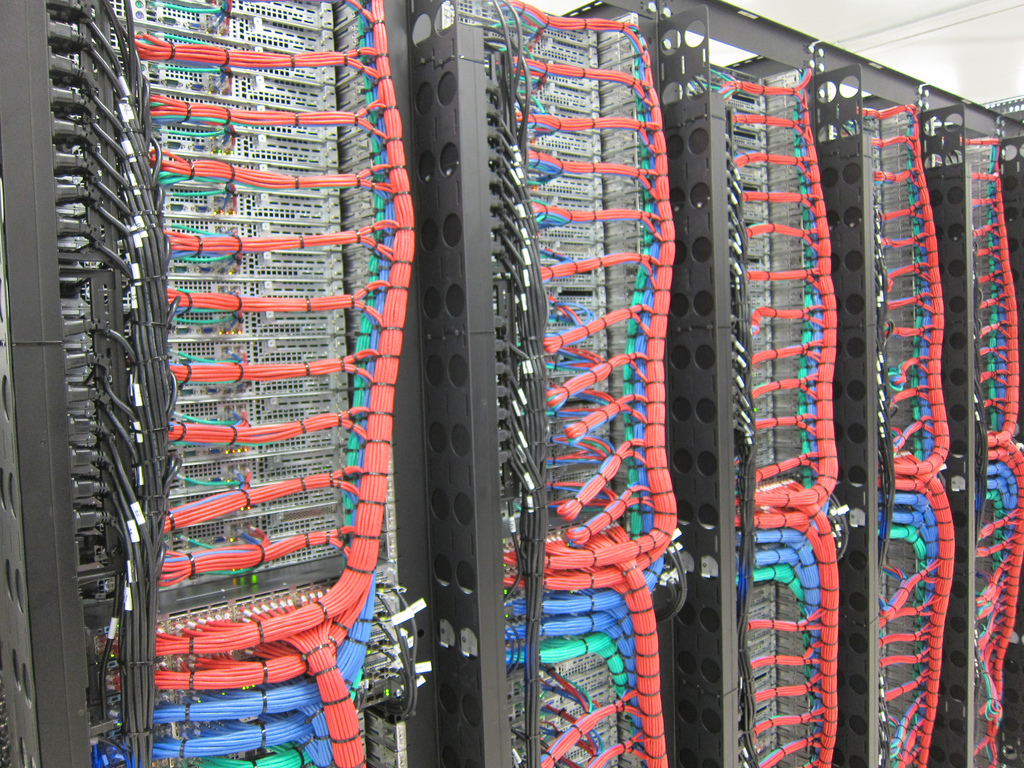
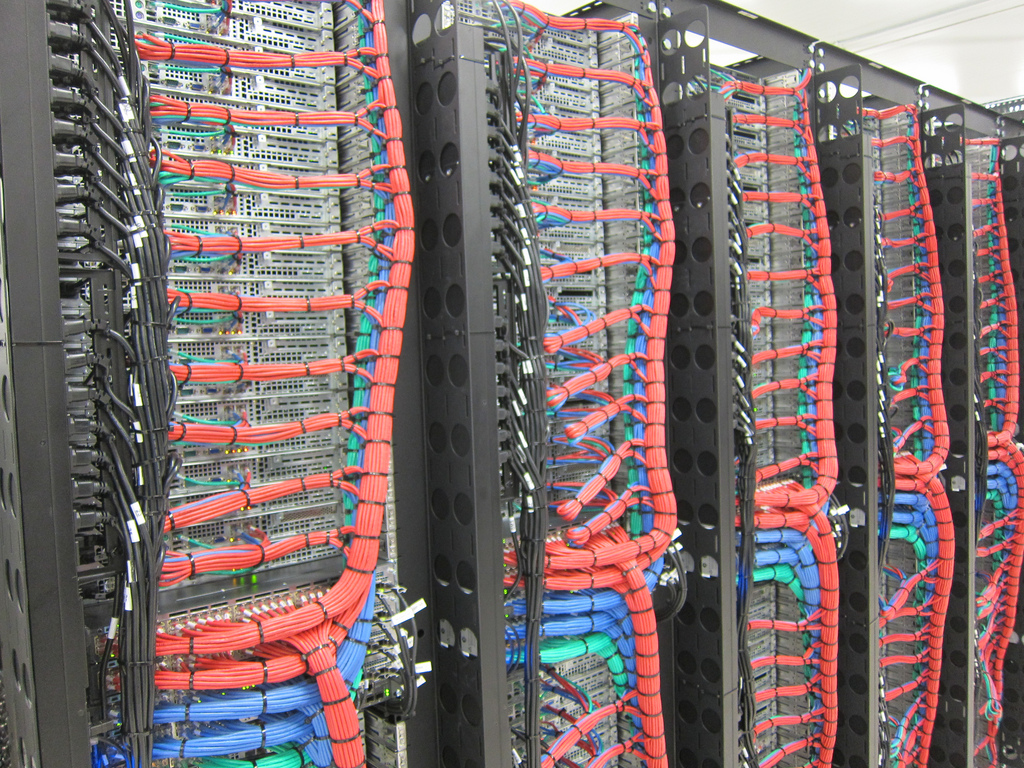
This is like one of those situations where you have a LOT of work setting up and managing something and people will never recognize the work, help, split the bill or be patient. People are so expected tech to “just click a button” and everything just works and is free that they aren’t even able to understand the complexity of what’s behind it all and the amount of work it is required to get “a simple file sync” to work.

 2·2 months ago
2·2 months agoAnd what about signal? If some gov founds a group chat they don’t like, will they take it down? How will they even know if all the contente is encrypted?
CSAM? More like copyright infringement. CSAM is the usual cheap excuse to shut down everything because of the obvious social implications.

 12·2 months ago
12·2 months agoWhile I don’t disagree with you, I don’t believe that if MTProto 2 was breakable govts would be putting the shit show they’re putting right now.
Telegram doesn’t use encryption. Everything is in clear text. Nobody needs a back door to get access. Not even governments. It’s all just out in the open
This isn’t even true, Telegram isn’t IRC. Like any modern application, uses SSL (encapsulated in MTProto) to protect connections. Govts will only have access if they manage to compromise those certificates, like your bank’s website.
Telegram are the ones making a promise. I’m not saying they’ve broken their promise (as evidenced by the arrest).
The fact that govts go after them kinda validates the promise. Unlike Signal.
This has nothing to do with the ability for the company to see what users do, but with the fact that govts can order Signal and others to hand user data, ban chats and whatnot while Telegram simply ignores requests like those.
Govts aren’t pissed about the fact that Telegram might be an accessory to a crime, they’re pissed because they can’t compromise it. Do you remember the FBI vs Apple situation, they wanted backdoors / access to E2EE stuff and Apple was refusing to provide and they went against one of the largest tech companies out there. Do you really believe that the US govt just went after Apple but wouldn’t go after a small company like Signal? This looks shady - almost like there’s a security vulnerability / backdoor in Signal they can use whenever they want.
I agree with you, but just think about this:
signal, a truly secure messenger, will comply with data requests and will send the authorities everything they have about a user, which is really not that much to begin with.
A govt asks Signal for info on a user, then Signal hands over a bunch of IP logs, metadata and a few encrypted messages that are still pending delivery or something on their servers.
Do you remember the FBI vs Apple situation, they wanted backdoors / access to E2EE stuff and Apple was refusing to provide and they went against one of the largest tech companies out there. Do you really believe that the US govt just went after Apple but wouldn’t go after a small company like Signal? This looks shady - almost like there’s a security vulnerability / backdoor in Signal they can use whenever they want.
Why would they go after the “not E2EE” chat but not after the “unbreakable and private” one? Telegram delivers trust, users trust that they won’t share any info to govts. Signal only delivers a promise that their E2EE will be enough to make the information govts get useless.
This whole Telegram story is absolutely unrelated to chat control
Chat control is exactly about baking backdoors and providing govts full access to chat logs etc. something that Telegram would never be okay with. They don’t even reply to govts requests most of the time, let alone be compromised at that level.
the answer from my perspective is quite simple. Noncompliance. If telegram had complied to local laws, like the others have and continue to do, he would not have gotten in trouble.
Exactly you’re getting there. Now let me ask something, if Facebook/Apple/Signal/Matrix comply with such laws how private are they? Those companies will happily censor chats and hand records to the govt, Telegram won’t.
Now you can argue that they do hand info the the govts but it is all encrypted and whatnot… do you really trust there aren’t backdoors there? Or cleaver ways to get around it like what we saw with push notifications or macOS analytics?
Govts are only after Telegram because they can’t infiltrate the company, ask for data etc. If Signal was really as secure and private like everyone says it is then their executives would already be in jail and whatnot for “enabling criminal activities”.
Telegram isn’t E2E encrypted and the telegram company can access all your messages, however, just think about the bigger picture there. How come that the E2E encrypted WhatsApp, Signal and whatnot never had their CEOs arrested for not moderating content / enabling criminal activity? Think about that.
First they obliterate telegram (most likely the only ones that would not comply and still offer service in Europe, Facebook and Apple would just comply, Signal would drop Europe) and a few days later they restart talks on this.













It your provider has some endpoint somewhere. The thing is, if you’ve law enforcement involved it doesn’t really matter is it’s WiFi calling or a cellular call, they’ll still be able to tie it to you.